Weak DMARC security policies are exploited by APT43
Advanced Persistent Threat (APT) group APT43, originating from North Korea and known for its espionage activities, is currently exploiting poorly configured or unconfigured DMARC policies. According to an article by BleepingComputer, APT43 uses these vulnerabilities to send fake emails impersonating legitimate journalists or researchers specializing in “East Asian affairs”.
The NSA has published two email samples that illustrate the techniques used by this North Korean group. These examples show how APT43 manipulates email headers and leverages weak DMARC policies to impersonate legitimate organizations, bypass security filters, and gain unauthorized access to sensitive information.
Who is APT43?
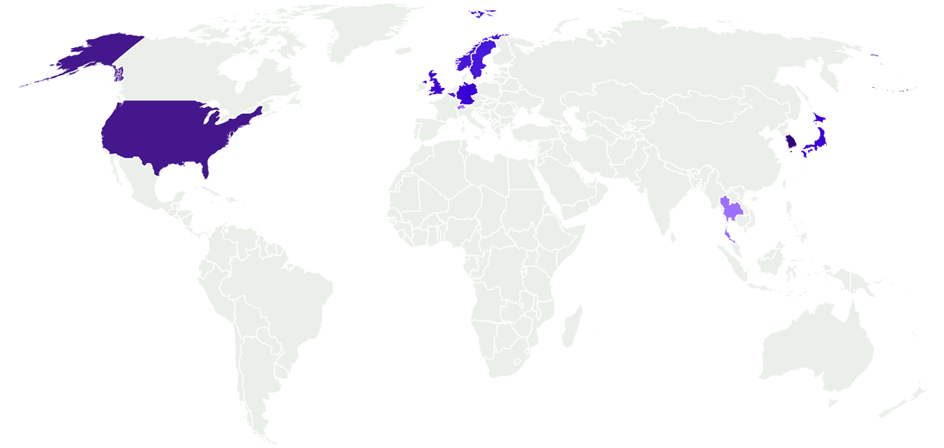
APT43, also known as Kimsuky, has its origins in North Korea and is active in the field of data theft and espionage on behalf of the North Korean government. Various sources indicate that the Group operate in Japan, South Korea, Thailand, USA, Vietnam and Europe.
Affected countries - https://mandiant.widen.net/s/zvmfw5fnjs/apt43-report
In the shadowy world of cyber threats, certain ransomware groups have distinguished themselves through their prolific activities and sophisticated attacks. Here, we delve into the top 5 ransomware groups of 2023, exploring their modus operandi and the unique threats they pose.
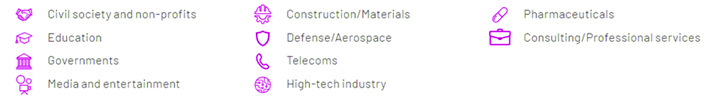
Industries affected - https://mandiant.widen.net/s/zvmfw5fnjs/apt43-report
Spear phishing campaigns
Spear phishing campaigns are the most frequently observed tactic. Fake domains and email addresses are integral to their social engineering strategies, which manipulate individuals to obtain sensitive data. These deceptive domains closely resemble legitimate websites and are used to harvest various types of information.
For instance, attackers create seemingly authentic login pages, such as those mimicking Microsoft, enticing users to enter their credentials. This information is then forwarded to the attackers and stored in a database, awaiting future use to gain unauthorized access to the company's systems.
Different elements, such as the malware used, vary slightly in each attack to prevent immediate identification of the hacker group involved. For example:
- VENOMBITE: A loader that drops malicious content on the system and executes the initial stage of the attack.
- BITTERSWEET: A backdoor that exploits program/system vulnerabilities to further infiltrate the device with malware or allow remote access.
What is DMARC?
To understand Domain-based Message Authentication, Reporting and Conformance (DMARC), in advance it is important to understand what exactly Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM) are.
SPF is a protocol that checks which IP addresses are legitimate and which addresses are authorized to send mails to your own domain.
SPF procedure - https://cyberhoot.com/cybrary/sender-policy-framework-spf/
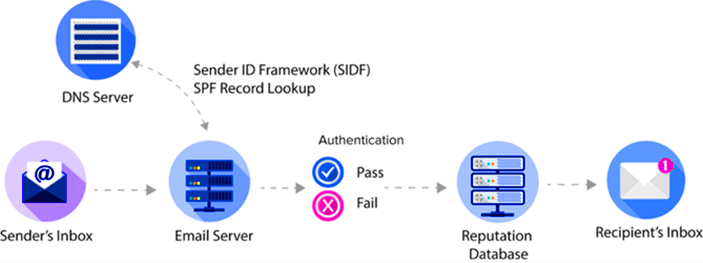
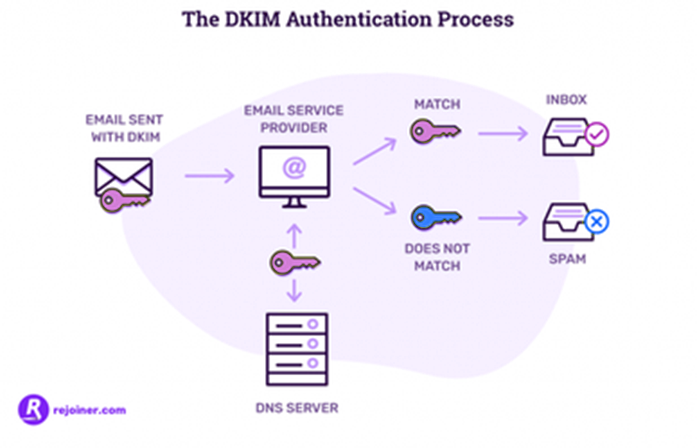
The DKIM protocol uses a public and a private key. The mail is signed by the private key when the mail is sent, creating a digital fingerprint. The associated public key, which is stored in the DNS server, can be used to check whether the sender of the mail is who they claim to be.
DKIM procedure - https://www.rejoiner.com/resources/what-is-a-dkim-record
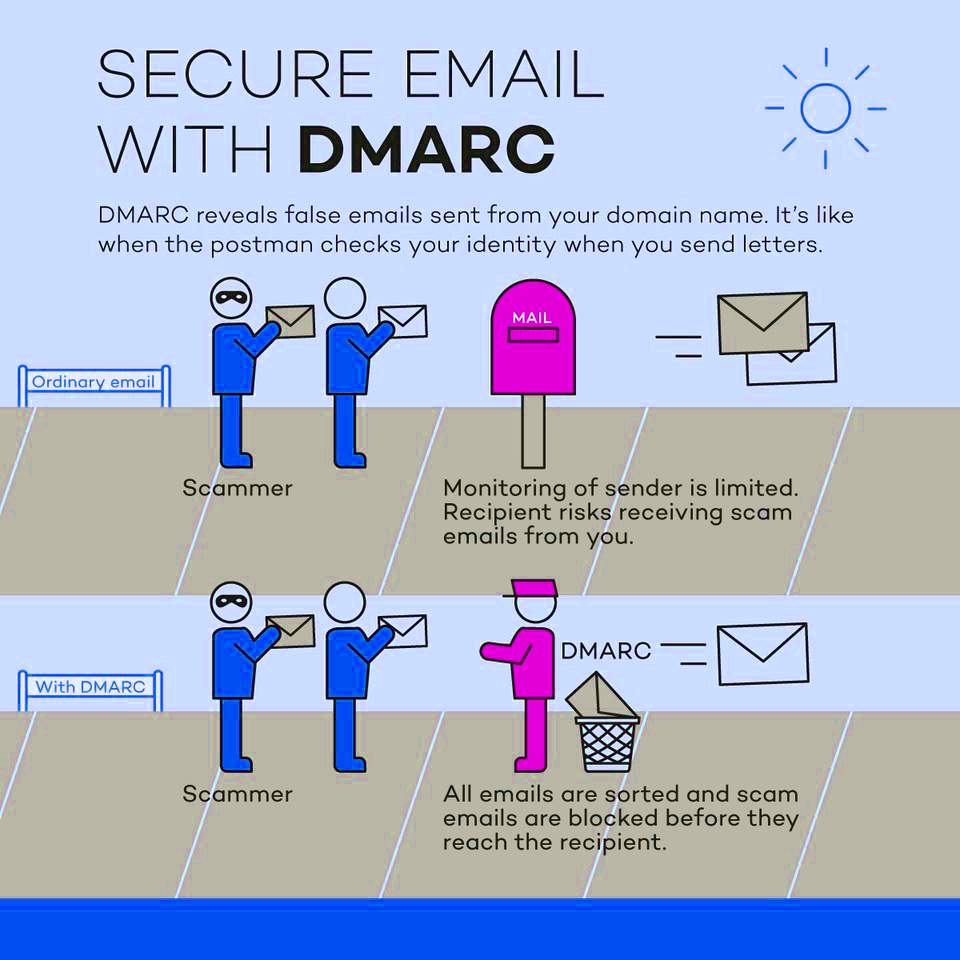
The DMARC protocol acts as a 'gatekeeper.' It is used to determine what should happen to emails that fail the authentication tests, namely SPF and DKIM. You can choose to quarantine, reject, or allow these emails. This process protects the company from spoofing attempts that try to impersonate trusted identities.
DMARC learns to differentiate between legitimate and malicious emails by analyzing previously received emails. These actions and findings are stored in the 'Think Tank', where a feedback mechanism continuously refines and updates the protocol to improve future decision-making.
What is the APT43 strategy?
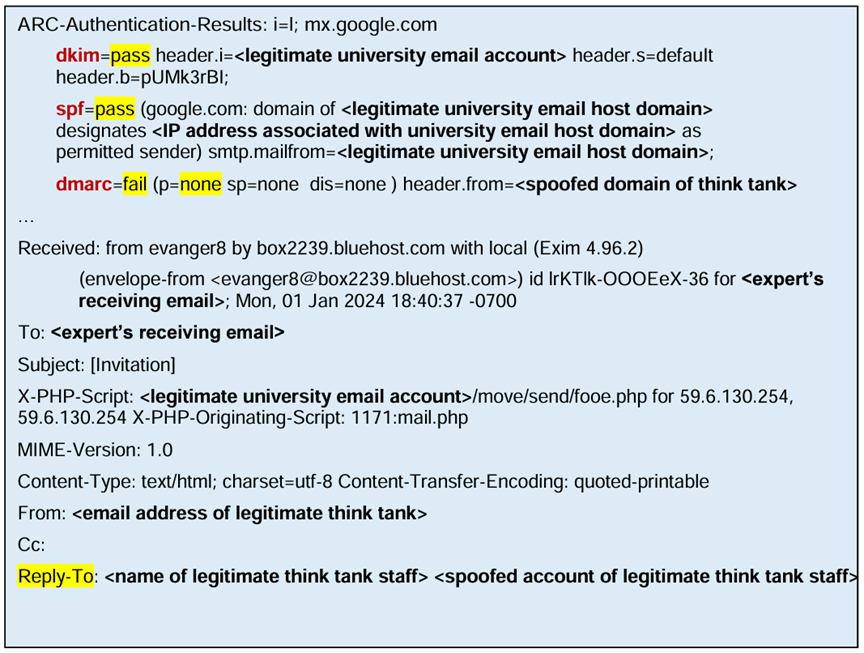
The NSA has released two sample emails showcasing the layout and header.
The first example was used at the end of 2023 and beginning of 2024. These were sent to USG officials and other international companies.
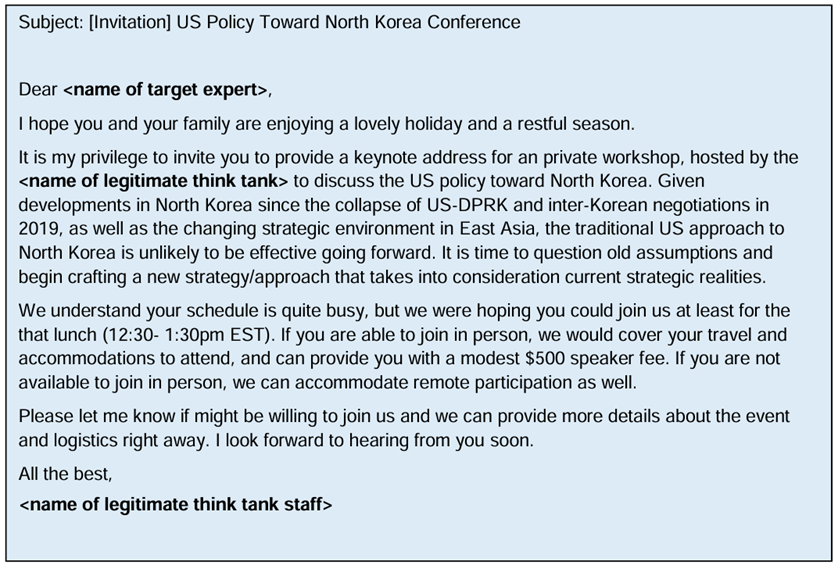
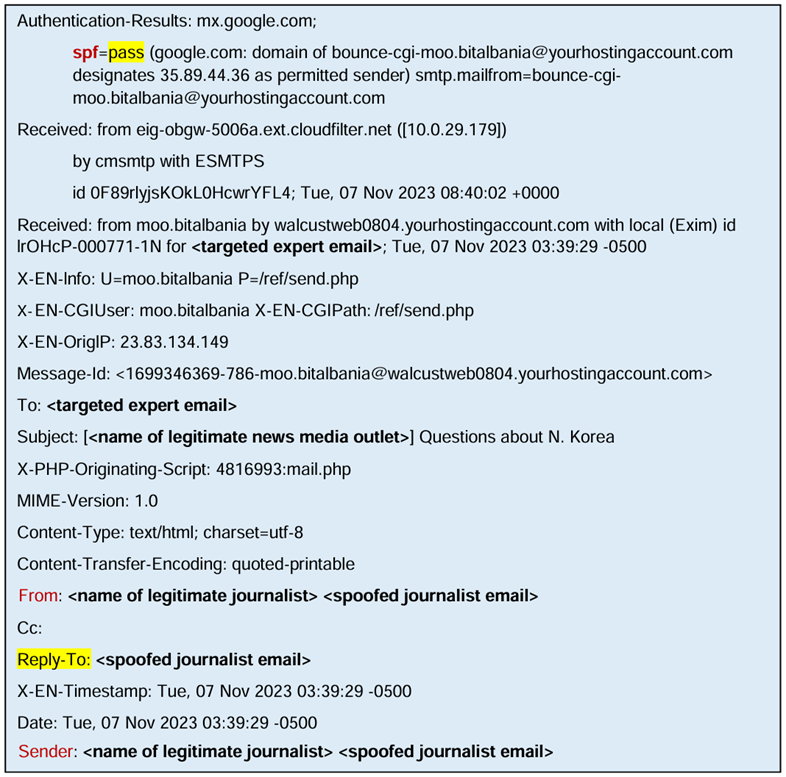
The header indicates that SPF and DKIM authentication were successful, confirming access to a legitimate mail client. However, the DMARC status shows a 'fail' because the sender's domain differs from the domain of previously known legitimate emails stored in the Think Tank.
The policy `p=none` means that despite the DMARC failure, no filtering measures (e.g., quarantine, reject) are enforced, allowing the email to reach the recipient's inbox. Notably, the 'Reply-To' field has been altered by the attackers, redirecting replies to an account under their control. This weak DMARC policy makes it difficult to identify the true sender domain, thereby concealing their identity.
In the second example, an authoring agency received spearphishing messages. APT43 posed as a legitimate journalist asking an expert on North Korea for comment. In addition, the supposed journalist asked for the expert's reply to be sent to a different, in this case fake, personal email address, as he does not have access to the original account.
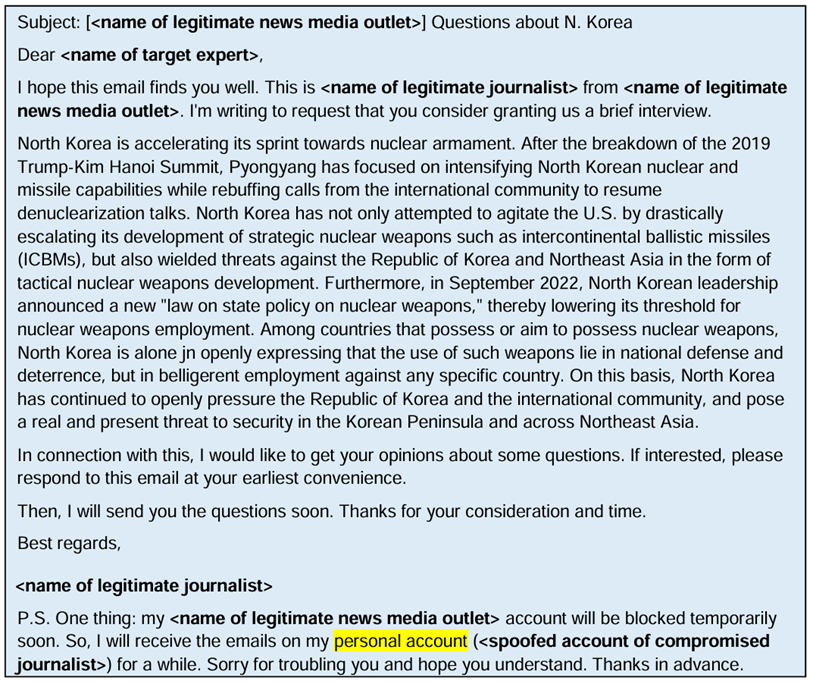
In this example, the DMARC policy is missing, which was exploited by the North Korean actor. Additionally, the SPF check was successful due to authentic IP address and the name of a legitimate journalist as well as the domain of the journalist's media company was used. Just like in the first example, an account controlled by APT43 was used for ‘Reply-To’.
How can the company be protected?
The FBI, Department of State, and NSA recommend enhancing existing DMARC security policies. These measures are in line with the Cybersecurity Cross-Sector Performance Goals (CPGs) developed by CISA and the National Institute of Standards and Technology (NIST).
In the previous examples, it became apparent that missing or weak DMARC policies can lead to problems, as in both cases a lack of action has the effect that the emails end up in a user's inbox.
The organizations mentioned above recommend setting the configured DMARC policy to "quarantine" or "reject" in order to ensure the highest possible level of security.
In addition to the measures mentioned above, it is also important that the target groups of the respective sectors are aware of and pay attention to different behaviors that may indicate malicious activities. Such behaviors include, for example
- An initially harmless communication, but which is followed by links or documentation with a malicious background - these links/documentation can also be sent from other email addresses than the one with which the communication exists
- When receiving documents, it is important not to activate the macros - especially not if this is explicitly requested
- Mail content that originates from already infected users
- Mails that follow if spear phishing attempts are not responded to
- Incorrect grammar, e.g. incorrect sentence structure
- Mail accounts with initially legitimate mail addresses, but which differ from the original - e.g. a slightly spoofed domain/name
Sources
- https://www.nsa.gov/Press-Room/Press-Releases-Statements/Press-Release-View/Article/3762915/nsa-highlights-mitigations-against-north-korean-actor-email-policy-exploitation/
- https://media.defense.gov/2024/May/02/2003455483/-1/-1/0/CSA-NORTH-KOREAN-ACTORS-EXPLOIT-WEAK-DMARC.PDF
- https://www.bleepingcomputer.com/news/security/nsa-warns-of-north-korean-hackers-exploiting-weak-dmarc-email-policies/
- https://apt.etda.or.th/cgi-bin/showcard.cgi?g=Kimsuky%2C%20Velvet%20Chollima
- https://thehackernews.com/2024/05/nsa-fbi-alert-on-n-korean-hackers.html
- https://malpedia.caad.fkie.fraunhofer.de/actor/apt43
- https://mandiant.widen.net/s/zvmfw5fnjs/apt43-report
- https://www.microsoft.com/en-us/security/blog/2024/02/14/staying-ahead-of-threat-actors-in-the-age-of-ai/
- https://mxtoolbox.com/dmarc/details/what-is-dmarc
- https://cyberhoot.com/cybrary/sender-policy-framework-spf/
- https://cyberhoot.com/cybrary/dkim/
- https://mxtoolbox.com/dmarc/details/what-is-dmarc
- https://twitter.com/uk_daniel_card/status/1759685711974871484?t=7BHPD7CVK0cVWVZryjMm6A
- https://twitter.com/osintindustries/status/1759722450126864465?t=7BHPD7CVK0cVWVZryjMm6A