CVE-2023-35078 - Ivanti zero-day
Critical Authentication Bypass Zero-Day in Ivanti Endpoint Manager Mobile (EPMM)
The cybersecurity landscape has recently been shaken by a significant vulnerability in Ivanti Endpoint Manager Mobile (EPMM), previously known as MobileIron Core. This authentication bypass vulnerability has had a notable impact, affecting 12 ministries in Norway and illustrating its potential for widespread damage.
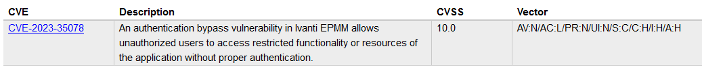
The flaw allows remote attackers to access specific API paths without the need for authentication, potentially exposing personally identifiable information (PII) such as names, phone numbers, and other details related to mobile devices. Additionally, it provides threat actors with the ability to alter configurations, including the creation of an EPMM administrative account for further system modifications.
Bleeping Computer reports that over 2,900 MobileIron user portals are presently exposed to vulnerabilities online, based on information from Shodan's Internet exposure scanning platform. This underscores the urgent necessity for remedial measures. An update that addresses this vulnerability is now widely available and it is strongly recommended that all Ivanti EPMM users install it without delay.

What is Ivanti EPMM?
This product serves as a comprehensive mobile management software engine, empowering IT departments to establish policies for mobile devices, applications and content. It provides capabilities for managing mobile devices, applications and content, thereby offering a holistic solution for mobile management needs.
Affected Versions
The vulnerability impacts all versions of Ivanti EPMM, including supported, unsupported, and end-of-life (EOL) releases, specifically releases 11.4, 11.10, 11.9, and 11.8. Even older versions are susceptible. Remedial patches for versions 11.10.0.2, 11.9.1.1 and 11.8.1.1 have been issued to mitigate this issue.
Exploitation Steps
The details surrounding the vulnerability in Ivanti EPMM remain somewhat shrouded, despite the company's efforts to provide information through a security advisory. Access to this advisory is currently restricted, requiring a login linked to Ivanti customer information. This means that the specifics of the vulnerability, including the steps to mitigate this threat, are not publicly available at this time.
However, it's important to note that despite the lack of public information, the vulnerability is reportedly easy to exploit. This highlights the urgency for users to apply the released patches, even in the absence of detailed public information about the vulnerability's exploitation.
Recommendations
To mitigate the risks associated with the recent vulnerability in Ivanti EPMM, it's crucial to take immediate action. The following steps are recommended:
- Install the latest Ivanti Endpoint Manager Mobile (formerly MobileIron) patches. These patches have been designed to safeguard systems from potential attacks exploiting this vulnerability.
- If you're unable to move away from EOL versions of the software, it's advised to switch off the appliance. This step, while potentially disruptive, is necessary to prevent the vulnerability from being exploited.